Synopsis:- Seminar, Praktische Informatik
- 2h each week, 2 SWS
- Students will present a selection of papers that will help you understand which threats exist, judge their significance and learn methods to defend your system against hackers. In addition you will explore the mathematical underpinnings of today's most common security tools and protocols.
Credits: In order to obtain credits for this seminar, participants are expected to: - Is possible for Bachelor.
- This seminar can be combined with "VL IT-Sicherheit Grundlagen" "Modul mit Seminar (BSEM)" zur Studienordnung Bachelor Informatik (Mono-Bachelor) [link]
- Attend regularly (at least 80%).
- Read each paper before the seminar, to be adequately prepared for discussion.
- Research an assigned subject; present major findings (30 min presentation; 15 min discussion).
- Presentations will be evaluated by two members of the audience at the end of each class (Bewertungskriterien-Seminarvortrag.pdf).
- Presenters summarize their in a term paper (German or English).
The paper should have 6 .. 10 pages (without counting the references), and should contain, abstract, motivation, related work, presentation of topic, conclusion and references. - Presentations may be given in German or English.
Prerequisites: - This seminar is suitable for students of all technical science disciplines who have previously completed courses "GdP" and "algorithms and data structures" or equivalent.
Topics (14/20 assigned): - ---Post Quantum Cryptography---
- Motivation und Survey (Grover, Shor, Timeline, Recommendations, Challenge) [pdf][NIST]
- Quantum Cryptography [pdf:Kapitel 4][pdf] (Carl)
- HASH-based Signatures [https][pdf] (Juri)
- FALCON [html][pdf][code]
- CRYSTALS-KYBER [html][pdf][git] (Tom F.)
- Attack on SIKE [sarwiki](sehr sehr anspruchsvoll)
---Private or Anonymous Communication: Tools, Building blocks & Limits--- - Password Hashing [html][git][pdf]
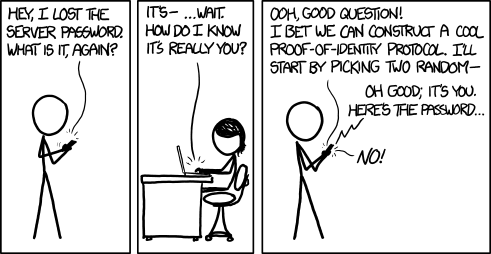
- One-TIME-Passwords [RFC6238][RFC4226][https]
- TOR the onion router [pdf][Attack: pdf][Datagram: pdf] (Anna)
- openPGP [RFC][Handbook GNUpg pdf]
- OTR Off-the-Record Messaging Protocol (version 3) [https]
- Signal [https][https][git] (Benjamin)
- Kryptografie mit elliptischen Kurven, ECDSA [pdf] {Clemens}
- Dragonfly Key Exchange [RFC]
- VeraCrypt [https][Probleme]
---Authentication: Techniques and Tokens--- - Mozilla Sync 1.5 API (Theory and Praxis) [https][https]
- WebAuthn / FIDO2 / U2F / [W3C][Video][https][WireShark-dissector][Demo]
- Direct Anonymous Attestation (DAA) [pdf]
- One TPM to Bind Them All: Fixing TPM 2.0 for Provably Secure Anonymous Attestation [pdf] (mathematisch anspruchsvoll)
---German electronic IDs--- - ePASS [ICAO] (Tom A.)
- nPA: PACE, EAC [TR-03110] (Jan)
- Digital Seal / JAB-Code [TR-03137-2]
---Payment--- - Bitcoin [whitepaper]
- Ethereum [whitepaper][guide]
- Monero [html] (Cole)
---Network--- - WLAN WPA-2 KRACK [https][pdf] (David)
- Bluetooth Pairing / KNOB-Attack [Specification / 4.2 Security, 4.2.2 Pairing] [https] (Philipp)
- TLS 1.3 [blog][RFC]
- TLS Revocation Mechanismen (CRL, OCSP, OCSP-stapling) in Theorie & Praxis [https]
- OpenVPN [pdf][https][https][https] (Mateusz)
- WireGuard VPN [pdf] (Israa)
- E2E Encryption for Zoom Meetings [pdf]
- --- (further topics are possible, also own interesting suggestions are welcome) ---
- Advanced Social Engineering Attacks [pdf] (Jonathan)
- Decentralized Identifiers [https]
- Verifying COVID-19-QR-Codes (QR -->base45-->uncompress-->cose-->CBOR) [https][git]
Syllabus: | Date | Presenters | Topic | Slides | | 16.10.23 | | dies academicus | | | 23.10.23 | | bootstrap / assignment of topics | [pdf] | | 30.10.23 | (optional) | consultation (fine tuning of topics) | | | 06.11.23 | all | elevator speeches | | | 13.11.23 | Jonathan
Tom F. | Advanced Social Engineering Attacks
CRYSTALS-KYBER | | | 20.11.23 | Carl
Juri | Quantum Cryptography
HASH-based Signatures | | | 27.11.23 | Tom A.
Jan | ePASS
nPA | | | 04.12.23 | David
Philipp | WLAN WPA-2 KRACK
Bluetooth Pairing / KNOB-Attack | | | 11.12.23 | Cole
Jonathan | Monero
Advanced Social Engineering Attacks | | | 18.12.23 | Tom A.
Jan | ePASS
nPA | | | 08.01.24 | Cole
Jonathan | Monero
Advanced Social Engineering Attacks | | | 15.01.24 | Mateusz
Israa | OpenVPN
WireGuard | | | 22.01.24 | | OMNISECURE 2024 | | | 29.01.24 | Anna
Benjamin
Jonathan | TOR
Signal
Advanced Social Engineering Attacks | | | 05.02.24 | | FIDO Plenum Madrid | | 12.02.24
| Tom A.
Mateusz
Israa
Benjamin
Anna | ePASS
OpenVPN
WireGuard
Signal
TOR | |
Recent / Incoming:
Further Readings (Research@SAR & Books): | |